I often get sick and tired of reading comments underneath a white-hat hacking tutorial, asking “how do I hack a Gmail”, “How to hack Facebook account”, etc by people that don't really understand the fundamentals of what they are asking. Then there are the RATters, bot masters, and others spreading Trojans with their back-doored, fake Facebook-Hacking programs, that prey on the ignorant people who downloads them.
While the “Master Hack” would be to find some insane Zero Day in the web application front end of the website's own servers, attacking them directly and pwning their massive database. That's just not going to happen. Surely not by anyone who has to ask “how to”. I'll tell you why. Google, Yahoo, Facebook (ANY of the big wheels in the cyber world) have entire teams of security specialists, constantly upgrading, monitoring, and researching their entire internal network infrastructure. Nothing connected to a network is ever 100% Secure, though, so I guess if you're a noob you may still have something like a 0.00000001% chance of accidentally finding a way in, before it is found and patched. They also have all the money in the world to ensure they are not running outdated or unsafe SQL versions or rules. Then we come to brute-forcing.. A semi direct attack. Anyone who has (in the last SEVERAL Years) tried guessing a password to an account on any of the big sites more than a few times and locked down the account after so many wrong guesses can quickly ascertain why it wouldn't be wise to throw 50 wrong guesses per second at one.
I could go on and on about impractical theories and misconceptions, but let's get to the fun part. I will go over how accounts are actually getting hacked into in the real world. This isn't a tutorial. Just an overview of various real world strategies, that don't take much technical know-how. It is more of a cleverness skill-set than a programing one, most of the time.
The majority of hacked accounts happen via simply stealing passwords to accounts. Once the attacker has the credentials, there are still often hurdles to overcome, in today's world. Most having to do with the security settings of the website and account, itself.. The attacker may be in a different country, and then the account may automatically lock down and require verification (via SMS, alternate email, etc). Not always, but I promise it does happen quite often. In this case he would have to be careful to use a proxy or vpn that matches the same location as the victim, or perhaps find a tor exit node via AdvOR that is of the same location. But the problem with using freely available proxies, vpns, and exit nodes are that they quickly become blacklisted by spammer usage and get flagged by the website. Also, many of the free proxies have very limited bandwith or restrictions. Most of this can be worked around for a few bucks, though.
The methods for stealing creds are far and wide, local and remote, and ever evolving in a war with the ever evolving security industry. The same industry that funds research into hacking their own systems and teaching the world how to break into them, in order to funnel more importance and money into their cause. But the economics and politics are a whole other subject.
PHISHING
The usual step-by-step for this technique is by uploading the fake, modified webpage, the script, and log to a web-hosting provider. But they are on the watch for that, these days and most phishing pages are actually being run on an apache server on the attacker's own box, with port 80 forwarded to it from the router and the obfuscated url actually pointing straight to their external ip (I know. Sad but true.), there are others hosted from a paid bullet-proof hosting service.
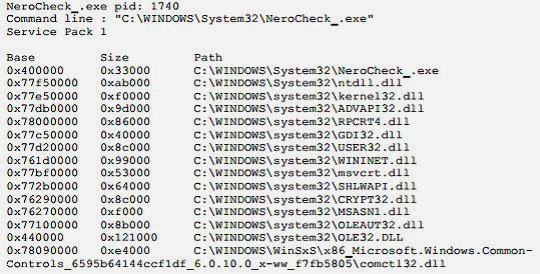
RATs, Keyloggers, Botnets, Stealers, and Other Trojans
Once an attacker has r00t, or even user privilege on the victim's machine, the server will report to the client what functions it was designed to do, this can (AND WILL) include keystrokes, screenshots, control of processes on the victim computer, remote desktop, and spy features, such as webcam and mic control (He can watch you and listen to you and save all of it!!!!).
Keyloggers, file-stealers, and password-stealers are pretty self explanatory. Usually the malicious exe is built to deliver to an ftp. Sometimes smtp. Botnets are usually specified for only specific functions and are geared more toward mass infection. The client side of a botnet is a builder executable and a control panel run on a local (or remote hosted) server and accessed via a web interface with a common browser.
MITM (Man in the Middle) Attack
In a MITM attack, the attacker is usually running an automated script that spoofs his MAC address, blocks usage of SSL encryption (via sslstrip, etc), and captures packets between machines. The attacker machine will basically tell the victim machine that he is the router and tell the router that he is the victim machine, and it will then pass along the packets to the destination device, like he was never there. SSL is usually blocked by a script that enforces http only, thus leaving creds passed along the network in plain text. Sometimes a favicon is even added that looks like a lock, so that it gives the impression of a safe, encrypted network protocol.
There are many variations to local network attacks. Some try to inject malicious iframes into the victim's browser or other client side attacks. Some don't capture creds or block SSL, but just capture the session cookie, losing access as soon as the victim logs out or it expires. Some even broadcast a fake access point. Most are done in public wifi networks. Some are corporate espionage type attacks, but by far, most are coffee shop/parking lot attacks by bored teenagers running automated scripts on a backtrack or kali linux machine.
The Local Attack
These are typically done by stalkers or nosy friends that find portable, easy to use forensic programs online, put them on a USB stick and play with someone's computer. They look for lots of things, including deleted files. But for this discussion, they look for account passwords saved by the browser of a naive user who doesn't clear his history, saved form data, passwords, etc.Guessing
I didn't get into SQL injection or other hacking on smaller sites and trying the same Creds you find there, onto the big sites, but it happens, too.
That concludes my overview of attack strategies that are common-place in the real world. Yes, there are many ways to get into things and many more will evolve. Some of these may be obsolete, in the future. But for the purposes of this discussion, this is how it is actually being done.
GJL
About the Author
I'm Gary. Though I have many names in many places, this is my true one. I am honored to have been invited by the RHA InfoSec to create content. I can't really go all the way into my experience, suffice to say my greatest teachers have been hours upon hours of trial, effort, information and second opinions.My skill-set is wide and varied and I am more a "Jack of all trades", rather than a specialist in any one category. I stay pretty busy with various projects (not all is computer related), but I will do my best to lend my time, effort, and knowledge. If I am busy or unable to answer any of your inquiries or handle your requests, for whatever reason, then I am sure Rafay, or Preston or any of the others can when they are able. Last but not least. I (PERSONALLY) do not want your likes, recognition, attention, traffic, or friends. Please save all of that for Rafay and the RHA Page. These guys have put this together, for you and deserve all recognition for it. Thank you.


















































![SQL Injection Basics - Union Based [Detailed Tutorial]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEjjQpa2wuMB-m5CXPVf71GUOkfiIOQA8KTyQ-_zfAl0SZa23UBN1QJaO2ZMGRDZlmDJTYf2jJ4ik3Xnj1locc38Yv9l6VMxTWt32s86JtXtLABDn20DRuAcbLPKMb9m2hc6PDmjIjvU-us/s72-c/SQL-Injection-Attack.jpg)


